Ransomware is running rampant these days, but there are several ways Windows 10 users and admins can protect their PCs. Here’s what to do.
CryptoLocker. WannaCry. Petya. Bad Rabbit. The ransomware threat isn’t going away anytime soon; the news brings constant reports of new waves of this pernicious type of malware washing across the world. It’s popular in large part because of the immediate financial payoff for attackers: It works by encrypting the files on your hard disk, then demands that you pay a ransom, frequently in Bitcoins, to decrypt them.
But you needn’t be a victim. There’s plenty that Windows 10 users can do to protect themselves against it. In this article, I’ll show you how to keep yourself safe, including how to use an anti-ransomware tool built into Windows 10.
Note that this article assumes that you’re already taking the basic precautions against malware in general, including running anti-malware software and never downloading attachments or clicking links in email from unknown senders and suspicious-looking email. Also note that this article has been updated for the Windows 10 October 2020 Update (version 20H2). If you have an earlier release of Windows 10, some things may be different.
Use Controlled Folder Access
Microsoft is concerned enough about ransomware that it built an easy-to-configure anti-ransomware tool directly into Windows 10; it’s included in all versions of Windows 10 released since October 2017. Called Controlled Folder Access, it protects you by letting only safe and fully vetted applications access your files. Unknown applications or known malware threats aren’t allowed through.
By default, the feature is not turned on, so if you want to protect yourself against ransomware, you’ll have to tell it to get to work. And you can customize exactly how it works by adding new applications to its whitelist of programs that can access files, and adding new folders in addition to the ones that it protects by default.
To switch it on, you’ll need to access Windows Security. There are several ways to get to it:
- You can click the up arrow to the left of the taskbar’s notification area, then click the Windows Security icon — a shield.
- From the Settings app (click the Start > Settings), you can select Update & Security > Windows Security.
- You can type windows security into the search box next to the Start button and select Windows Security from the flyout screen that appears on the right.
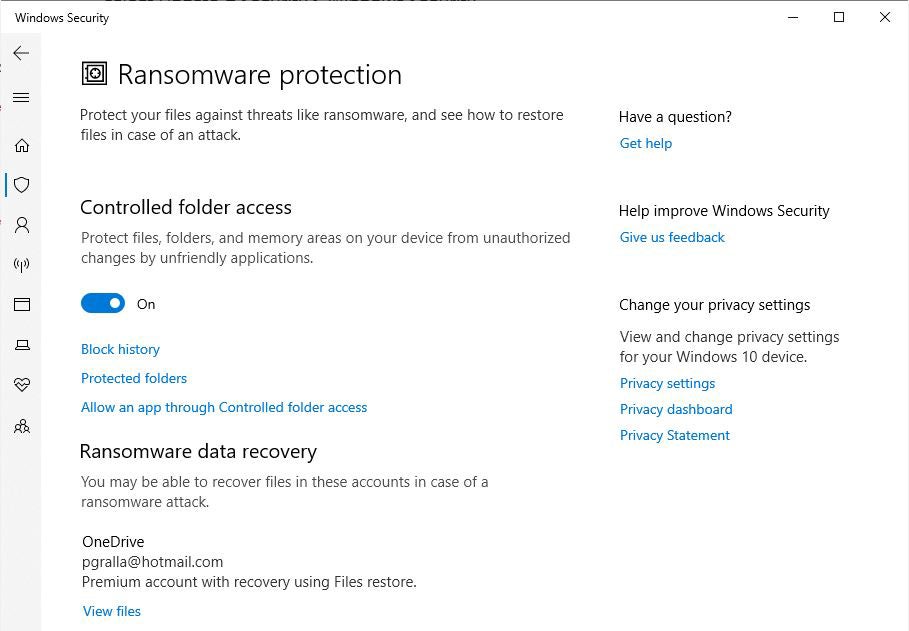
However you do it, once there, select Windows Security > Virus & threat protection. Scroll down to the “Ransomware protection” section and click Manage ransomware protection. From the screen that appears, under “Controlled folder access,” toggle the switch to On. You’ll get a prompt asking if you want to make the change. Click Yes.
IDG
You shouldn’t leave it at that and feel safe yet, because there’s a chance that you have folders you’d like to protect that the feature ignores. By default, it protects Windows system folders (and folders underneath them) like C:\Users\YourUserName\Documents, where YourUserName is your Windows user name. (In addition to Documents, other Windows system folders include Desktop, Music, Pictures and Videos.)
But all your other folders are fair game for any ransomware that makes its way onto your PC. So if you use Microsoft’s OneDrive cloud storage, for example, any OneDrive folders and files on your PC aren’t protected. Given that Microsoft is trying to move everyone it can onto OneDrive, this is a surprising omission.
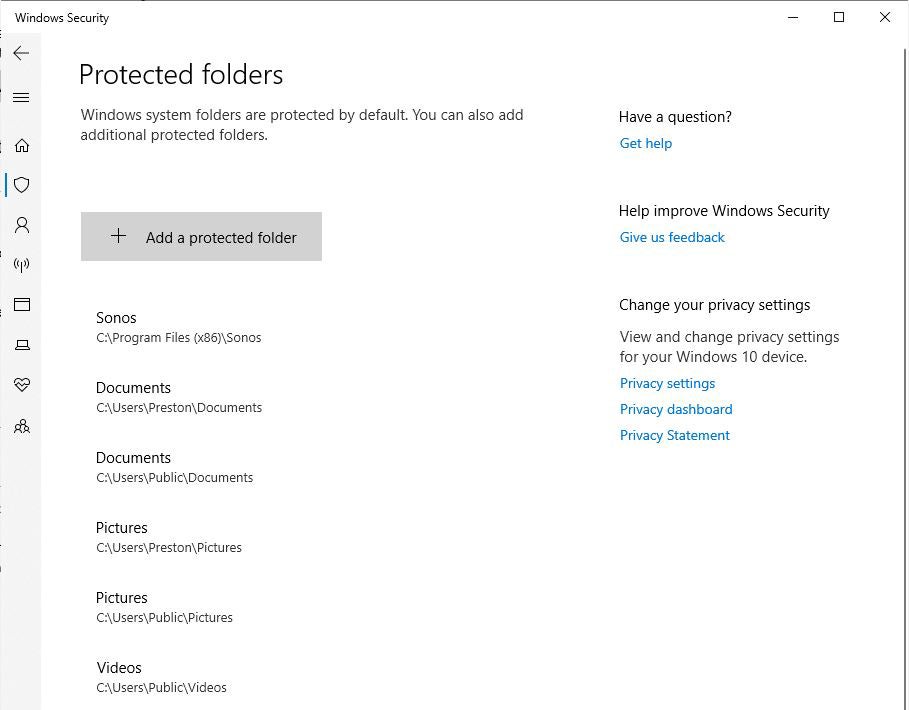
To add folders you want protected, click the Protected folders link that appears after you switch on Controlled Folder Access. A prompt appears asking if you want to make the change. Click Yes. Click the Add a protected folder button that is on top of the list of protected folders that appears, then navigate from the screen that appears to the folder you want to protect and click Select Folder.
IDG
Continue to add folders in this way. Remember that when you add a folder, all folders underneath it are protected as well. So if you add OneDrive, for example, there’s no need to add all of the folders underneath it.
If you decide at any point to remove a folder, get back to the “Protected folders” screen, click the folder you want to remove, and then click Remove. Note that you won’t be able to remove any of the Windows system folders that are protected when you turn the feature on. You can only remove the ones that you’ve added.
Microsoft determines which applications should be allowed access to protected folders, and unsurprisingly, among them is Microsoft Office. Microsoft hasn’t published a list of which applications are allowed, though, so consider taking action to let applications you trust access your files.
To do it, go back to the screen where you turned on Controlled Folder Access and click Allow an app through Controlled folder access. A prompt appears asking if you want to make the change. Click Yes. From the screen that appears, click Add an allowed app, navigate to the executable file of the program you want to add, click Open, and then confirm you want to add the file. As with adding folders to the list of protected folders, you can remove the app by getting back to this screen, clicking the application you want to remove, then clicking Remove.
Hint: If you’re not sure of where executable files are located for programs you want to add to the whitelist, look for the folder name with the program’s name in the Windows\Program Files or Windows\Program Files (x86) folders, then look for an executable file in that folder.
Back up… but do it properly
The whole point of ransomware is to hold your files hostage until you pay to unlock them. So one of the best protections from ransomware is to back up your files. That way, there’s no need to pay the ransom, because you can easily restore your files from the backup.
But when it comes to ransomware, not all backups are created equal. You need to be careful about choosing the right backup technique and service. It’s a good idea to use a cloud-based storage and backup service rather than only backing up to a drive attached to your PC. If you back up to a drive attached to your PC, when your PC gets infected with ransomware, the backup drive will likely be encrypted along with any other disks inside or attached to your PC.
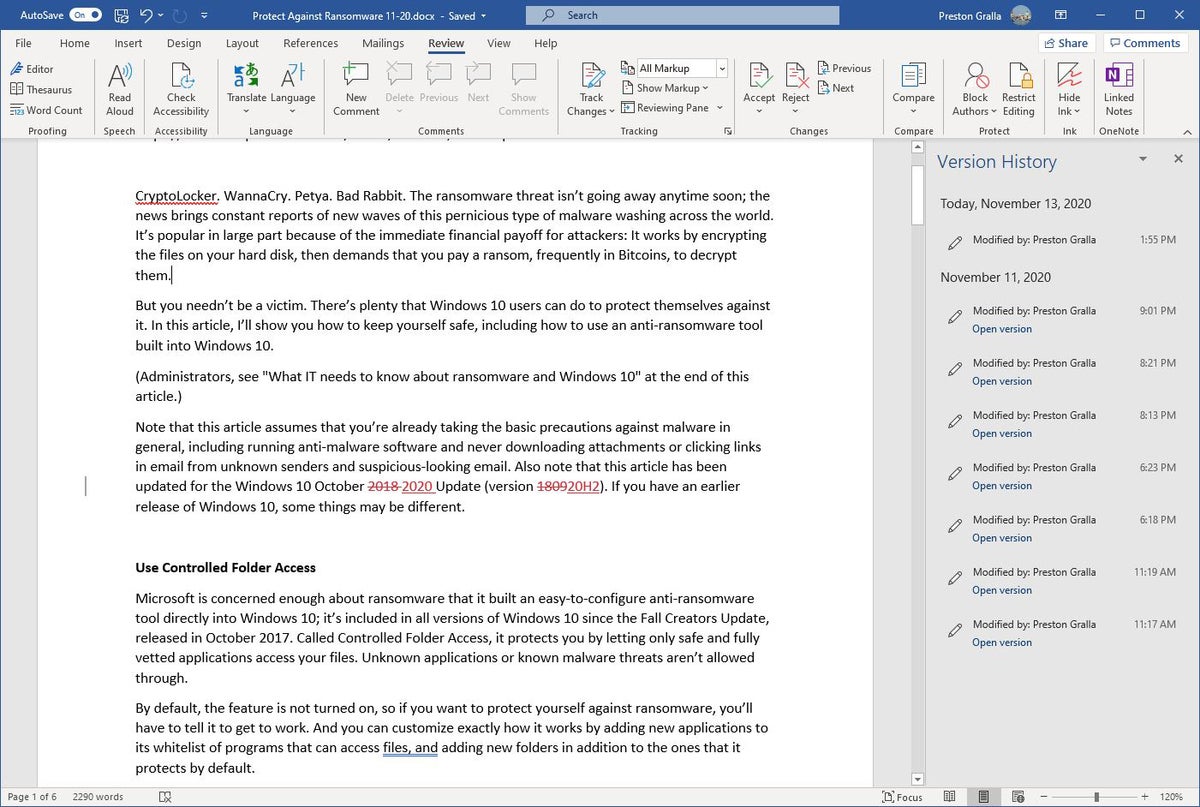
Make sure that your cloud-based storage and backup uses versioning — that is, it keeps not just the current version of each of your files, but previous ones as well. That way, if the most current version of your files gets infected, you can restore from previous versions.
Most backup and storage services, including Microsoft OneDrive, Google Drive, Carbonite, Dropbox and many others, use versioning. It’s a good idea to get familiar with the versioning feature of whichever service you use now, so you can easily restore files in a pinch.
IDG
Get free ransomware protection
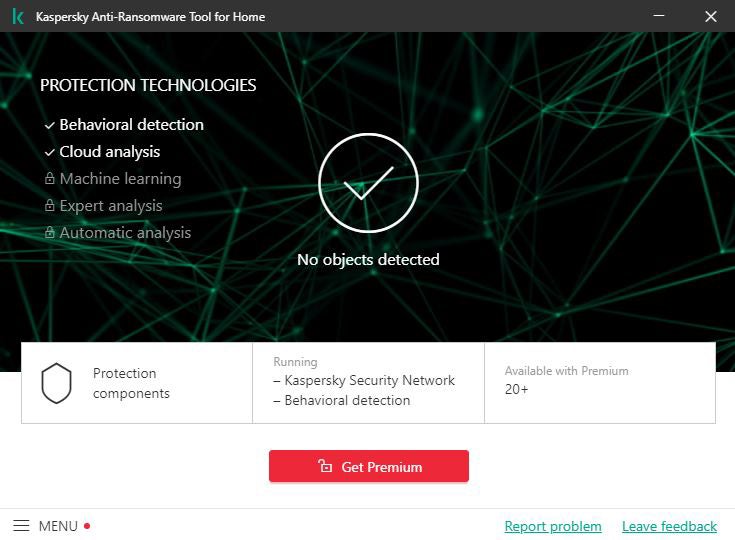
Just about any anti-malware program includes built-in anti-ransomware protections, but there are several programs that promise to specifically target ransomware. A number of them are paid, but there are also some free options, such as those I’m listing here.
Bitdefender offers free decryption tools that can unlock your data if you’ve been attacked by ransomware and it’s being held ransom. It can only decrypt data that’s been encrypted with certain specific pieces of ransomware, including MoMoCrypt, WannaRen and several others. And Kaspersky offers anti-ransomware software for free for both home and business users.
IDG
Stay patched
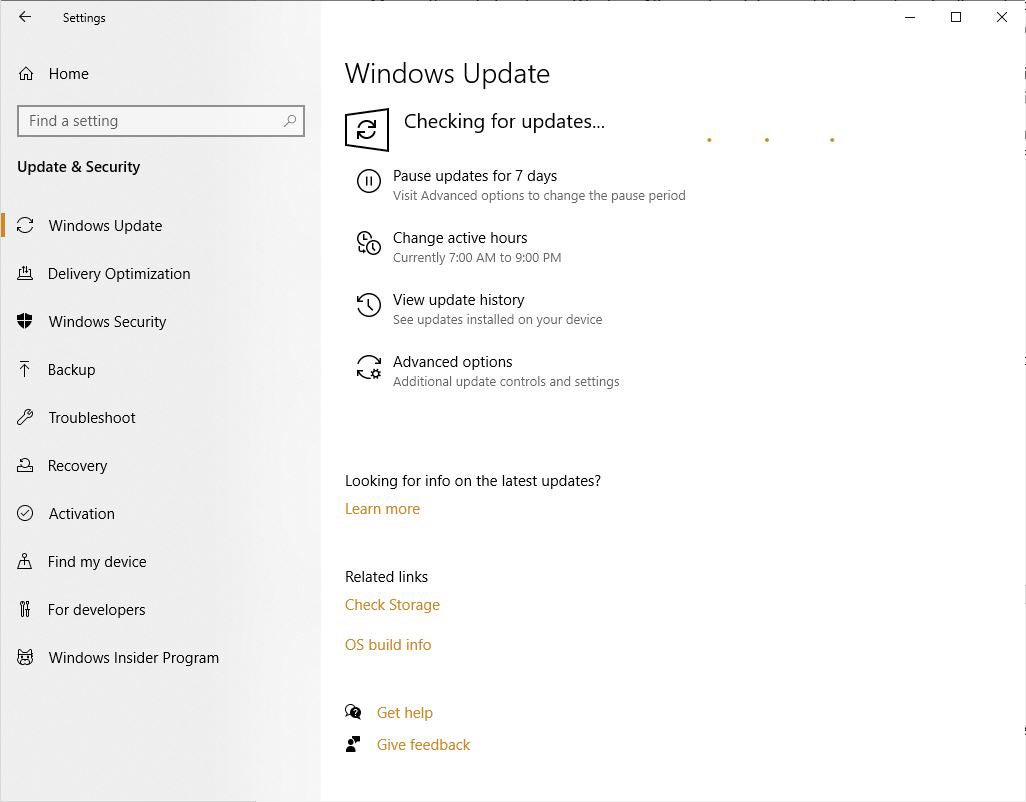
Microsoft regularly releases Windows 10 security patches, and they’re automatically applied via Windows Update. But if you hear about a ransomware outbreak, you shouldn’t wait for Windows Update to work — you should immediately get the update yourself so that you’re protected as soon as possible. And it’s not just Windows updates you want to get. You also want to make sure Windows Security, Microsoft’s built-in anti-malware tool, has the latest anti-malware definitions.
To do both, go to Settings > Update & Security > Windows Update and click the Check for updates button. (If updates are already waiting for you, you’ll see them listed instead of the Check for updates button.) If Windows finds updates, it installs them. If it requires a reboot, it will tell you.
IDG
You need to worry not just about Windows staying patched, but other software as well. If you use an anti-malware program other than Windows Security, make sure it and its malware definitions are up to date.
And the other software on your PC should be kept up to date as well. So check how each piece of software gets updated and make sure to update each one regularly.
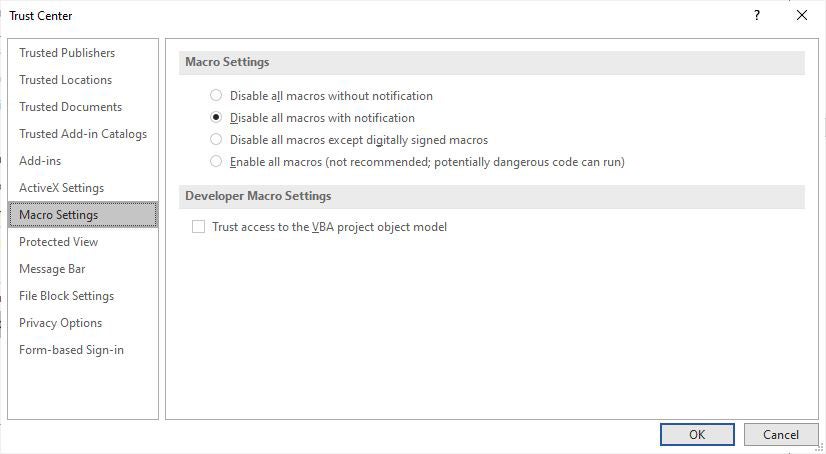
Disable macros in Microsoft Office
Ransomware can be spread via macros in Office files, so to be safe you should turn them off. To do it, when you’re in an Office application, select File > Options > Trust Center > Trust Center Settings and select either Disable all macros with notification or Disable all macros without notification. If you disable them with notification, when you open the file you’ll get a message warning that the macros were disabled and letting you turn them on. Only turn them on if you’re absolutely sure they’re from a safe, trusted source.
IDG
What IT needs to know about ransomware and Windows 10
There’s plenty that IT can do to keep companies free from ransomware. The most obvious: Apply the latest security patches to not just all PCs in an organization, but all servers and any other enterprise-level hardware.
That’s just a start, though. IT needs to disable the notoriously insecure SMB1 Windows networking protocol. Multiple ransomware attacks have spread through the 30-year-old protocol; even Microsoft says it should be used by no one, ever.
The good news is that Windows 10 version 1709, released in October 2017, finally did away with SMB1. But that’s only for new PCs that have come out since then or clean installs of version 1709 or later. PCs that were updated from earlier versions of Windows still have the protocol built in.
There are multiple places IT can go to get help to turn it off. A good place to start is the SMB Security Best Practices document from US-CERT, run by the U.S. Department of Homeland Security. It recommends disabling SMB1, and then “blocking all versions of SMB at the network boundary by blocking TCP port 445 with related protocols on UDP ports 137-138 and TCP port 139, for all boundary devices.”
The Microsoft support article “How to enable and disable SMBv1, SMBv2, and SMBv3 in Windows and Windows Server” offers details about how to turn off the protocol. It recommends killing SMB1 but keeping SMB2 and SMB3 active, and only deactivating them for temporary troubleshooting. For the most up-to-date and detailed information about turning off SMB1, go to the Microsoft TechNet article “Disable SMB v1 in Managed Environments with Group Policy.”
Administrators who have upgraded their users to Windows 10 version 1709 or later can use the Controlled Folder Access feature (covered earlier in this article) to stop ransomware from encrypting files and folders. They can use the Group Policy Management Console, the Windows Security Center or PowerShell to turn on controlled folder access for users on a network, customize which folders should be protected, and let additional applications access the folders beyond the Microsoft defaults. For instructions, go to the Microsoft article “Enable Controlled folder access” to turn it on, and to “Customize Controlled folder access” to customize which folders should be protected and which applications should be allowed through.
One potential issue with Controlled Folder Access is that it might block apps that users typically use from accessing folders. So Microsoft recommends using audit mode first, to see what will happen when Controlled Folder Access is turned on. For information about how to do it, go to Microsoft’s “Use audit mode to evaluate Windows Defender Exploit Guard features.”
As noted above, Office macros can spread ransomware. So IT can use Group Policy to block macros in Office 2016 and 2019. For advice on how to do it, go to the TechNet post “New feature in Office 2016 can block macros and help prevent infection.”
Bottom line
The good news in all this: Windows 10 is the most secure version of Windows yet released, and as explained in this article, it now has specific anti-ransomware features built right into it. Follow the advice we’ve outlined here to keep the ransomware threat at bay.
This article originally appeared on ComputerWorld.